Chain code
In the following article, we will thoroughly explore Chain code and its impact on various aspects of everyday life. From its influence in the workplace to its relevance in the personal sphere, Chain code has been the subject of numerous studies and debates over the years. Through a comprehensive analysis, we will examine the many facets of Chain code, its implications in today's society, and how it has evolved over time. Additionally, we will explore the different perspectives and opinions of experts in the field, with the aim of providing a comprehensive and detailed view on this relevant topic.
A chain code is a lossless compression based image segmentation method for binary images based upon tracing image contours. The basic principle of chain coding, like other contour codings, is to separately encode each connected component, or "blob", in the image.
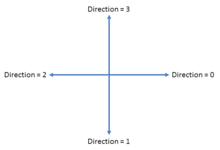
For each such region, a point on the boundary is selected and its coordinates are transmitted. The encoder then moves along the boundary of the region and, at each step, transmits a symbol representing the direction of this movement.
This continues until the encoder returns to the starting position, at which point the blob has been completely described, and encoding continues with the next blob in the image.
This encoding method is particularly effective for images consisting of a reasonably small number of large connected components.
Variations
Some popular chain codes include:
- the Freeman Chain Code of Eight Directions (FCCE)
- Directional Freeman Chain Code of Eight Directions (DFCCE)
- Vertex Chain Code (VCC)
- Three OrThogonal symbol chain code (3OT)
- Unsigned Manhattan Chain Code (UMCC)
- Ant Colonies Chain Code (ACCC)
- Predator-Prey System Chain Code (PPSCC)
- Beaver Territories Chain Code (BTCC)
- Biological Reproduction Chain Code (BRCC)
- Agent-Based Modeling Chain Code (ABMCC)
In particular, FCCE, VCC, 3OT and DFCCE can be transformed from one to another
A related blob encoding method is crack code. Algorithms exist to convert between chain code, crack code, and run-length encoding.
A new trend of chain codes involve the utilization of biological behaviors. This started by the work of Mouring et al. who developed an algorithm that takes advantage of the pheromone of ants to track image information. An ant releases a pheromone when they find a piece of food. Other ants use the pheromone to track the food. In their algorithm, an image is transferred into a virtual environment that consists of food and paths according to the distribution of the pixels in the original image. Then, ants are distributed and their job is to move around while releasing pheromone when they encounter food items. This helps other ants identify information, and therefore, encode information.
In use
Recently, the combination of move-to-front transform and adaptive run-length encoding accomplished efficient compression of the popular chain codes. Chain codes also can be used to obtain high levels of compression for image documents, outperforming standards such as DjVu and JBIG2.
See also
References
- ^ Freeman, Herbert (June 1961). "On the Encoding of Arbitrary Geometric Configurations". IRE Transactions on Electronic Computers. EC-10 (2): 260–268. doi:10.1109/TEC.1961.5219197.
- ^ Liu, Yong Kui; Žalik, Borut (April 2005). "An efficient chain code with Huffman coding". Pattern Recognition. 38 (4): 553–557. Bibcode:2005PatRe..38..553K. doi:10.1016/j.patcog.2004.08.017.
- ^ Bribiesca, Ernesto (February 1999). "A new chain code". Pattern Recognition. 32 (2): 235–251. Bibcode:1999PatRe..32..235B. doi:10.1016/S0031-3203(98)00132-0.
- ^ Sanchez-Cruz, Hermilo; Rodríguez-Dagnino, Ramón M. (September 2005). "Compressing bilevel images by means of a three-bit chain code". Optical Engineering. 44 (9). 097004. Bibcode:2005OptEn..44i7004S. doi:10.1117/1.2052793.
- ^ Žalik, Borut; Mongus, Domen; Liu, Yong-Kui; Lukač, Niko (July 2016). "Unsigned Manhattan chain code". Journal of Visual Communication and Image Representation. 38: 186–194. doi:10.1016/j.jvcir.2016.03.001.
- ^ a b c Mouring, Matthew; Dhou, Khaldoon; Hadzikadic, Mirsad (2018). "A Novel Algorithm for Bi-Level Image Coding and Lossless Compression based on Virtual Ant Colonies". Proceedings of the 3rd International Conference on Complexity, Future Information Systems and Risk. COMPLEXIS 2018. Vol. 1. pp. 72–78. doi:10.5220/0006688400720078. Retrieved 2022-07-06.
- ^ a b Dhou, Khaldoon (January 2020). "A new chain coding mechanism for compression stimulated by a virtual environment of a predator–prey ecosystem". Future Generation Computer Systems. 102: 650–669. doi:10.1016/j.future.2019.08.021. S2CID 202783274.
- ^ a b Dhou, Khaldoon (2018). A Novel Agent-Based Modeling Approach for Image Coding and Lossless Compression Based on the Wolf-Sheep Predation Model. ICCS 2018. Computational Science – ICCS 2018. LNCS. Vol. 10861. pp. 117–128. doi:10.1007/978-3-319-93701-4_9.
- ^ a b Dhou, Khaldoon; Cruzen, Christopher (May 2021). "A highly efficient chain code for compression using an agent-based modeling simulation of territories in biological beavers". Future Generation Computer Systems. 118: 1–13. doi:10.1016/j.future.2020.12.016. S2CID 232023010.
- ^ a b Dhou, Khaldoon; Cruzen, Christopher (December 2019). "An Innovative Chain Coding Technique for Compression Based on the Concept of Biological Reproduction: An Agent-Based Modeling Approach". IEEE Internet of Things Journal. 6 (6): 9308–9315. doi:10.1109/JIOT.2019.2912984. S2CID 150025529.
- ^ a b Dhou, Khaldoon (June 2019). "An innovative design of a hybrid chain coding algorithm for bi-level image compression using an agent-based modeling approach". Applied Soft Computing. 79: 94–110. doi:10.1016/j.asoc.2019.03.024. S2CID 126831246.
- ^ Sanchez-Cruz, Hermilo; Lopez-Valdez, Hiram H. (January 2014). "Equivalence of chain codes". Journal of Electronic Imaging. 23 (1). 013031. Bibcode:2014JEI....23a3031S. doi:10.1117/1.JEI.23.1.013031. S2CID 41897871.
- ^ Rosenfeld, Azriel; Kak, Avinash C. (1982). "Chapter 11 - Representation". Digital Picture Processing. Vol. 2 (2nd ed.). Academic Press. p. 220. Bibcode:1982dpp..book.....R. doi:10.1016/B978-0-12-597302-1.50010-4. ISBN 0-12-597302-0. ISBN 0-12-597301-2, 0-12-597302-0
- ^ Žalik, Borut; Lukač, Niko (January 2014). "Chain code lossless compression using move-to-front transform and adaptive run-length encoding". Signal Processing: Image Communication. 29 (1): 96–106. doi:10.1016/j.image.2013.09.002.
- ^ Rodríguez-Díaz, Mario A.; Sánchez-Cruz, Hermilo (July 2014). "Refined fixed double pass binary object classification for document image compression". Digital Signal Processing. 30: 114–130. doi:10.1016/j.dsp.2014.03.007.